 root / sudo
root / sudo
If you are reading this you are likely aware that the administrator on Linux/Unix systems is referred to as root. The root account is the account on which all system processes run and should be the only account that can write to the main filesystem.
Because most of us started our computing lives out using Microsoft Windows there has always been a notion that it is better to be the administrator of the system. Unfortunately this is one of the major causes of insecurity in computing and opens up your system to instability. As most Linux users will tell you, only log in as root to perform maintenance on your system and never log in to a graphical or desktop session using root.
Ubuntu takes this one step further. Rather than asking users not to login as root, they have locked the root account and default to using sudo. As a side effect users have /sbin, /usr/sbin and /usr/local/sbin as part of their $PATH environmental variable, meaning they can see commands that users can not normally see.
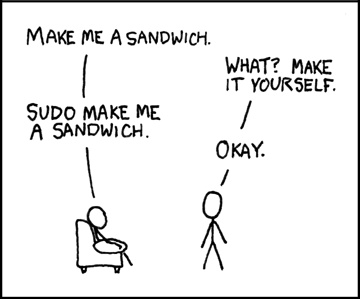
What is sudo?
It is a tool to allow you to execute a command as root, without logging in as root. Its name is derived from a related command su “do”. su is the command to switch user and is most frequently used to run commands as root. So in essence, sudo is ‘switch user do <command>.
It provides several key benefits;
- It logs all commands run using it
- It logs failed attempts to authenticate using it
- It can be restricted in a much more detailed way than simply using root, i.e. per user permissions
- It can be used with the user’s login password rather than distributing the root password
The latter is the case with Ubuntu so that users are prevented from logging in permanently as root but can temporarily elevate themselves to root to run the required system command. Ubuntu is configured to allow members of the admin group have access to commands via sudo. Anyone else attempting to run a command in this manner will have their attempt logged and mailed to the system administrator(s).
How is it used?
When running certain commands in a terminal you will notice that they will either not work or will return no information. Try running
fdisk -l
The above command will have run as your own regular user and should not have returned a value. Now try running it with sudo, to run it with root privilege
sudo fdisk -l
This time you should be prompted for your password and on entering it you will see a listing of all of your hard disk partitions, something only possible with root privilege.
What about graphical applications
Although it isn’t a great idea to run any old application as root, there are some that need to such as package managers and system configuration tools. Synaptic Package Manager for example. You can run the command ‘synaptic’ but you will receive errors about starting without administrative privileges. But if you were to prefix this with gksu (for Gnome) or kdesu (for KDE) you will first be prompted for your root password and then the application would run correctly.
So there you have it. That little prefix to your commands lets you run just what needs to be run as root and keeps your system secure and stable. And even for distributions that do not require the use of sudo, it can’t be a bad habit to get into
Further reading:
sudo
Wikipedia entry on sudo
Ubuntu article on sudo
Source: Linux Forum
Popular Posts:
- None Found
