 Many Java application server use a keystore as a repository of their certificates and in general all Java applications use the one supplied with the JDK itself, Let’s see what is it and how to work with it.
Many Java application server use a keystore as a repository of their certificates and in general all Java applications use the one supplied with the JDK itself, Let’s see what is it and how to work with it.
A keystore is a repository of security certificates, that can hold your keys and certificates and encrypt them all with a password. In other words, a keystore is just like a hashtable which has an alias that identifies a certificate and then the certificate itself.
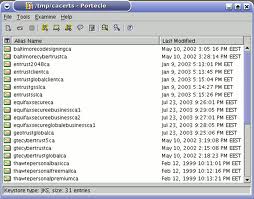
The Java JDK maintains a CAC keystore in jre/lib/security/cacerts. JDKs provide a tool keytool to manipulate the keystore.
Another way to manage this kind of certificate is Portecle a graphical tool that can help in these operation.
Keytool
Keytool manages a keystore (database) of cryptographic keys, X.509 certificate chains, and trusted certificates. These examples are for the keytool shipped with Java SE 6.
Create a private key
keytool -genkeypair -alias mycert -keyalg RSA -keysize 1024 -dname "CN=localhost,OU=Home,O=Home,L=SL,S=WS,C=LK" -keypass mypkpassword -keystore mykeystore.jks -storepass mystorepassword |
CN –> Common Name
OU –> Organizational Unit
O –> Oranization
L –> Locality
S –> State
C –> Country
This generates a private key and stores it in the given keystore [mykeystore.jks]. In case you didn’t have a keystore then the above will create a new keystore for you with a private key.
Also note the two parameters -keypass and -storepass. -keypass is the password used for your private key and -storepass is the password used for keystore.
View the contents of a Keystore
This is an example with a CACERT provided by Java:
root@laptop:/etc/ssl/certs/java# keytool -list -keystore cacerts |
This command give an output like this (the defualt keystore password is changeit):
Enter keystore password: Keystore type: JKS Keystore provider: SUN Your keystore contains 141 entries startcom_ltd, Oct 2, 2009, trustedCertEntry, Certificate fingerprint (MD5): 08:7C:58:1F:52:2B:44:B4:3B:79:CD:01:F8:C5:C3:C9 startcom_certification_authority, Oct 2, 2009, trustedCertEntry, Certificate fingerprint (MD5): 22:4D:8F:8A:FC:F7:35:C2:BB:57:34:90:7B:8B:22:16 gte_cybertrust_global_root, Oct 2, 2009, trustedCertEntry, Certificate fingerprint (MD5): CA:3D:D3:68:F1:03:5C:D0:32:FA:B8:2B:59:E8:5A:DB go_daddy_class_2_ca, Oct 2, 2009, trustedCertEntry, |
To get more verbose output you can use the -v flag
Import a Certificate
One of the most common things is to import new certificates into your keystore.
For example, import in your keystore the root CA of Verisign, you can get the VeriSign’s root certificate from here.
Copy all the text from there to a new file and name it as verisign-demo-root-cert.pem.
Now, let’s add it to yout keystore.
keytool -importcert -v -noprompt -trustcacerts -alias verisigndemocert -file verisign-demo-root-cert.pem -keystore mykeystore.jks -storepass mystorepassword |
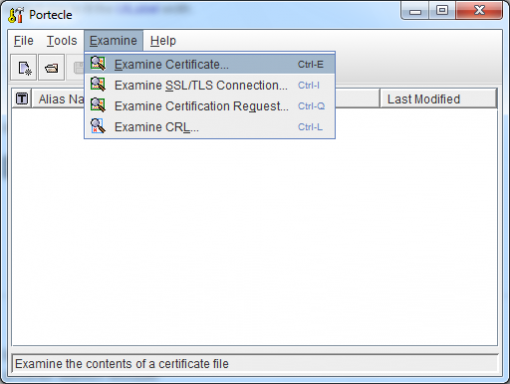
Portecle
Portecle is a user friendly GUI application for creating, managing and examining keystores, keys, certificates, certificate requests, certificate revocation lists and more.
To use Portecle just:
1. Download the Portecle at here
2. Unzip the downloaded archive.
3. Open the extracted folder and start the Portecle GUI by “java -jar portecle.jar”
This will start the Portecle Gui from where you can open a keystore, examine a certificate, export and do other things much more easily than the keytool command.
References:
http://blog.facilelogin.com/2008/03/keystore-management-part-i.html
http://portecle.sourceforge.net/
http://ykyuen.wordpress.com/2010/07/05/portecle-keystore-and-certification-manager/
Popular Posts:
- None Found

If you want to replace keytool with a GUI tool then you can also use CERTivity.
http://www.edulib.com/products/keystores-manager/
It can handle different types of keystores (JKS, JCEKS, PKCS12, BKS, UBER, Windows) and digital signatures.
How to check the actual file location, by actual i mean .pem file