Today I propose you an interesting topic based on an article by Jacob Cook first published on https://citizenweb.is/
Over the past few years, a handful of different encrypted messaging systems have cropped up and gained prominence, notably Cryptocat and the OTR specification. Now a newcomer to the scene proposes a different way of thinking about encrypted communication, one that borrows from its more well-known older brother, BitCoin.
A project has been started that intends to recreate BitCoin’s decentralized P2P model for seamless message encryption and transmission.
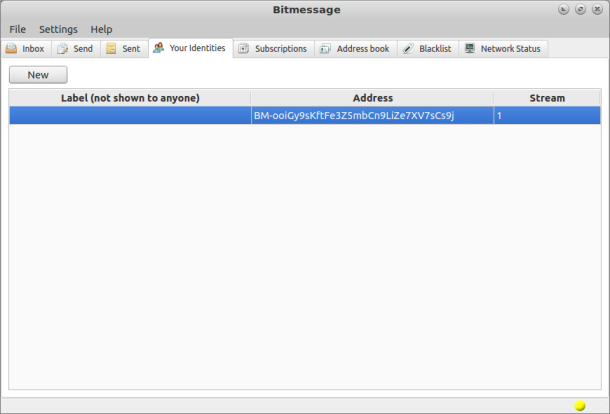
BitMessage was started by Jonathan Warr en late last year and has now made it up to version 0.2.4. One of the most prominent strengths of the BitMessage system is how it enforces anonymity. Similar to how BitCoin allows one to send money to anonymous recipients without advertising metadata to others, BitMessage communicates via simple addresses generated from public keys, which need not be tied to a specific user’s identity.
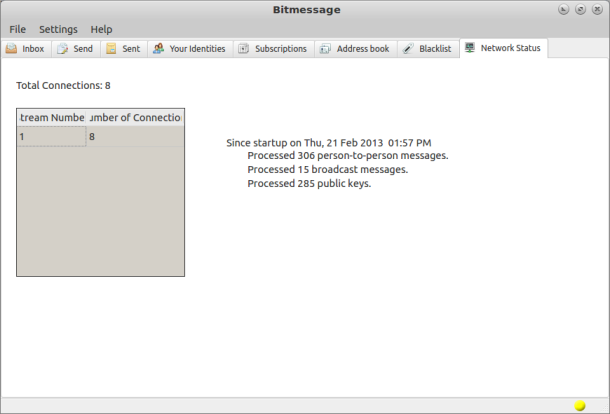
Similar to BitCoin’s operation, BitMessages are sent out to all users who are connected to the system. Then, each client attempts to decrypt the message if it is intended for that client. Messages not intended for that client will simply be ignored. This presents major issues with scalability, as has been noted with BitCoin’s system. BitMessage responds to this by proposing a so-called “stream” infrastructure. Once the network gets to be a certain size, it will break itself into separate streams. Clients will only connect to a stream if they have a message to send or receive somewhere in that stream. This follows a decentralized model in which certain machines act as “parents” for streams and will aid in advertising the clients it has in its stream, and facilitating the connection.
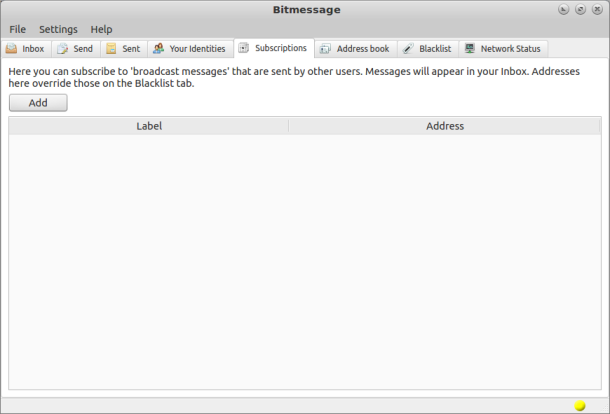
More than just a decentralized and anonymous messaging system, BitMessage appears to also have limited social messaging capability. As messages are sent out as broadcasts, it would be easy for individuals to simply “subscribe” to the messages that are sent by users they like, then receive them in a manner similar to Twitter, identi.ca or Tent feeds. If this operation is easily worked in to BitMessage clients, it could provide a push for other projects in the decentralized social networking space to put a stronger focus on privacy and security.
Downloading and Installation on Linux
- Open a terminal and test that you have python, OpenSSL and git installed by opening a terminal and testing them with the following commands :
python --version openssl version git --version
- If one or more of the items are not installed, install them, on .deb systems (Debian/ubuntu based systems) use
-
# sudo apt-get install python python-qt4 openssl git
- In the terminal, change to the directory you want the Bitmessage folder in (but don’t create the bitmessage folder yet!)
- Clone the git repository by entering the following command:
# git clone https://github.com/Bitmessage/PyBitmessage
- Change to the PyBitmessage source directory by entering the command
cd PyBitmessage/src - Start PyBitmessage by entering the command
python bitmessagemain.py - Optionally create a startup script that runs the command
python PyBitmessage/src/bitmessagemain.py
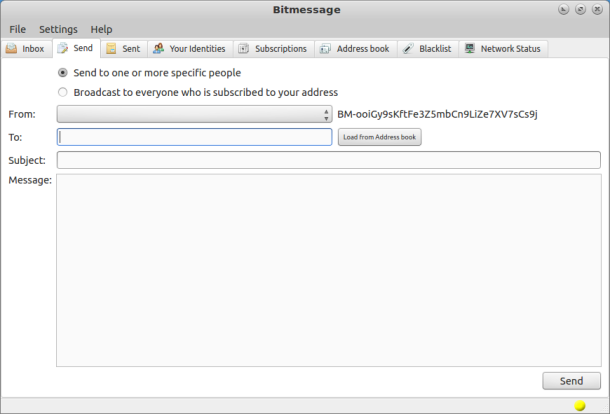
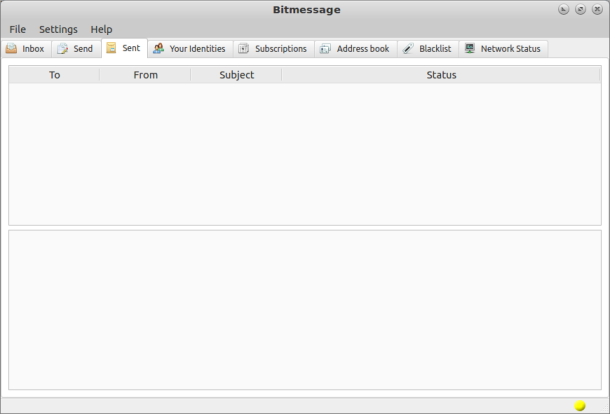
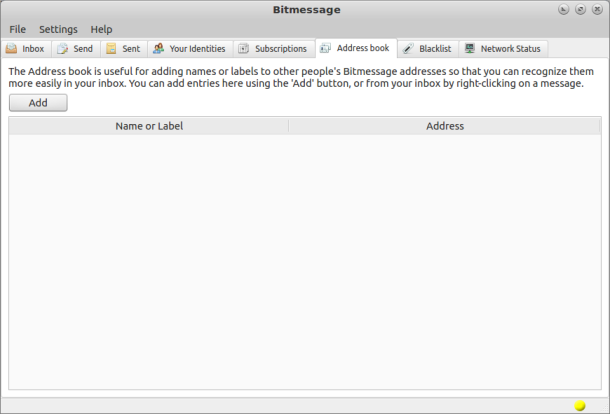
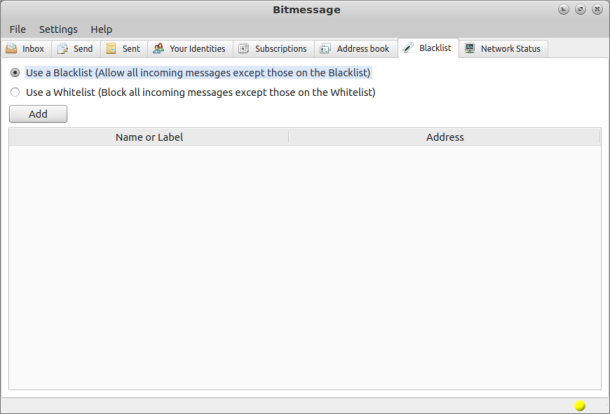
And this is how the application looks like:
Conclusions
BitMessage is a secure very secure paranoid email system which when run from the command line connects to many remote peer network clients. Anonymity is all but guaranteed it cannot be traced and the message despite working through the peer network can not be hacked intercepted or altered in any way. BitMessage is heavily secure but does not require pgp as this is built in using hash instead, making it simpler to use once you have an address to send to and from, this forming part of the security protocol used. As no mail server is used there is no requirement or function to login, This mail delivery system can be used in a variety of ways, however it cannot send mail using the SMTP (Simple Mail Transfer Protocol) it is completely different and does not transpose at all, BitMessage at least for now does not handle attachments, not a bad thing overall as attachments can hide trojans, but this does limit the scope of how this system can be used.
References:
Setting Up And Using Bitmessage – An Encrypted Communications Platform Based On Bitcoin
Bitmessage – Decentralized Email Networking
Popular Posts:
- None Found
