
Original article by Dominik Zajac published on his blog
In the time of free wifi and free internet connections in every hotel, bar or cafe you should be sure your connections are secure. In some cases you can’t trust the connection but you need to go online and read some mails or share some documents. In this case some basic tools like SSH and Firefox can help you to build a secure connection to a known computer in the internet you can trust (for example your own root server).
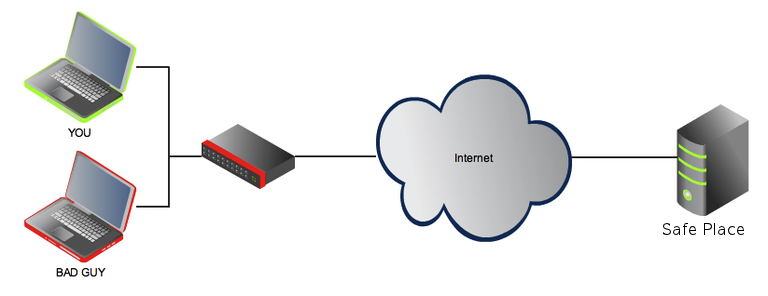
To make more clear what I am talking about i created this small diagram to make it more easy for me to explain what I am doing with this SSH connection and how I can benefit from it.
Let’s say I am connected with a public network or wifi access point. There are many people around me using the same connection and I don’t know the provider of the network very well. What I can do to get a secure connection is to open a SSH tunnel to my known machine and send all the traffic I am generating with my web browser through this tunnel.
This can be done with a SSH command like this:
ssh -D 8080 username@host |
What this command does is explained in the man pages of the ssh command:
-D [bind_address:]port Specifies a local “dynamic” application-level port forwarding. This works by allocating a socket to listen to port on the local side, optionally bound to the specified bind_address. Whenever a connection is made to this port, the connection is forwarded over the secure chan- nel, and the application protocol is then used to determine where to connect to from the remote machine. Currently the SOCKS4 and SOCKS5 protocols are supported, and ssh will act as a SOCKS server. Only root can forward privileged ports. Dynamic port forwardings can also be speci- fied in the configuration file. IPv6 addresses can be specified with an alternative syntax: [bind_address/]port or by enclosing the address in square brackets. Only the superuser can forward privileged ports. By default, the local port is bound in accordance with the GatewayPorts setting. However, an explicit bind_address may be used to bind the connection to a specific address. The bind_address of “localhost” indicates that the listening port be bound for local use only, while an empty address or `*’ indicates that the port should be available from all interfaces. |
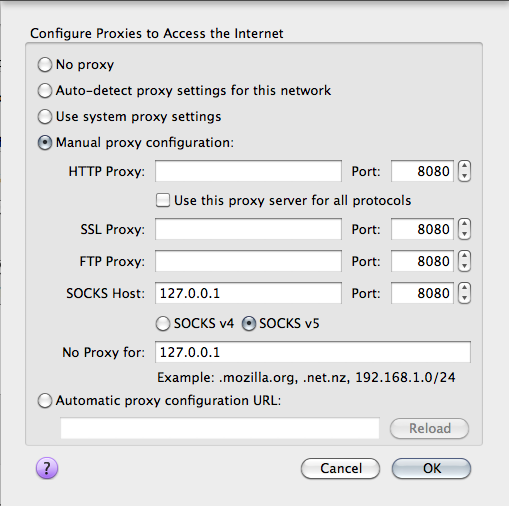
Now I have a local port (8080) where I can send my traffic trough. Only one thing I need to do now is to reconfigure my Firefox to use this port and connection and be sure DNS requests are sent through this secure connection as well.
Open the about:config page and set the following boolean.
network.proxy.socks_remote_dns; default boolean true |
If you want a possibility to activate and deactivate this proxy configuration with one click there are several firefox addons for managing proxy configurations like QuickProxy or FoxyProxy.
Popular Posts:
- None Found

++. I use it all the time!
Your a, an usage is wrong.
http://wordinfo.info/unit/3431/ip:1
Thanks Adam, i think that the original writer is German, I’ve corrected some a/an.
very useful info..
could you please tell in order to use this ssh setup as proxy , do i have to use static ip for my home pc or do i have to purchase a virtual privater server and use it as proxy.. or any other method for this..
Yes, you must have a static IP that you can reach via ssh.
So a computer at home with a static IP (or betetr an IP that you know), or a VPS are both good solutions.
You need to check out dynamic DNS services from dyndns or noip. They are free as long as you do not abuse them.
You can use Dynamic DNS service to avoid having to pay for a Static IP Address.
The most well known service is DynDNS: http://www.dyndns.com/
They offer a well written How-To: http://www.dyndns.com/support/kb/dyndns.html
Other services are available both free, and non-free, which may offer additional services:
http://dnslookup.me/dynamic-dns/
ciao linuxari, ottimo articolo (come sempre del resto).
volevo suggerire anche l’uso di tsocks per far confluire attraverso il proxy SOCKS anche il traffico dei software da riga di comando, così come descritto in un mio post sul mio blog.
Grazie per il commento e la dritta 😉
Vi ho conosciuto da poco e devo dire che siete fenomenali!
Ottimo articolo!
Consigliati!